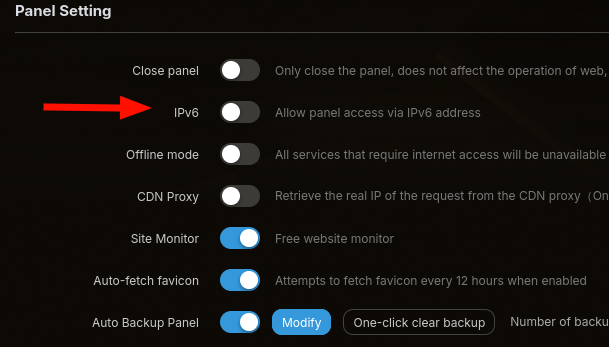
Turning ipv6 in the panel was the 1st thing i did after installing aapanel.
ipv6 is also disabled on server level.
/www/server/nginx/conf/nginx.conf
`user www www;
worker_processes auto;
error_log /www/wwwlogs/nginx_error.log crit;
pid /www/server/nginx/logs/nginx.pid;
worker_rlimit_nofile 51200;
stream {
log_format tcp_format '$time_local|$remote_addr|$protocol|$status|$bytes_sent|$bytes_received|$session_time|$upstream_addr|$upstream_bytes_sent|$upstream_bytes_received|$upstream_connect_time';
access_log /www/wwwlogs/tcp-access.log tcp_format;
error_log /www/wwwlogs/tcp-error.log;
include /www/server/panel/vhost/nginx/tcp/*.conf;
}
events
{
use epoll;
worker_connections 51200;
multi_accept on;
}
http
{
include mime.types;
#include luawaf.conf;
include proxy.conf;
default_type application/octet-stream;
server_names_hash_bucket_size 512;
client_header_buffer_size 32k;
large_client_header_buffers 4 32k;
client_max_body_size 256m;
sendfile on;
tcp_nopush on;
keepalive_timeout 60;
tcp_nodelay on;
fastcgi_connect_timeout 300;
fastcgi_send_timeout 300;
fastcgi_read_timeout 300;
fastcgi_buffer_size 64k;
fastcgi_buffers 4 64k;
fastcgi_busy_buffers_size 128k;
fastcgi_temp_file_write_size 256k;
fastcgi_intercept_errors on;
gzip on;
gzip_min_length 1k;
gzip_buffers 4 16k;
gzip_http_version 1.1;
gzip_comp_level 5;
gzip_types text/plain application/javascript application/x-javascript text/javascript text/css application/xml application/json image/jpeg image/gif image/png font/ttf font/otf image/svg+xml application/xml+rss text/x-js;
gzip_vary on;
gzip_proxied expired no-cache no-store private auth;
gzip_disable "MSIE [1-6]\.";
limit_conn_zone $binary_remote_addr zone=perip:10m;
limit_conn_zone $server_name zone=perserver:10m;
server_tokens off;
access_log off;
server
{
listen 888;
server_name phpmyadmin;
index index.html index.htm index.php;
root /www/server/phpmyadmin;
location ~ /tmp/ {
return 404;
}
#error_page 404 /404.html;
include enable-php.conf;
location ~ .*\.(gif|jpg|jpeg|png|bmp|swf)$
{
expires 30d;
}
location ~ .*\.(js|css)?$
{
expires 12h;
}
location ~ /\.
{
deny all;
}
access_log /www/wwwlogs/access.log;
}
include /www/server/panel/vhost/nginx/*.conf;
}
`!<
/www/server/panel/vhost/nginx/0.default.conf
`server {
listen 80 default_server;
listen 443 default_server;
ssl_reject_handshake on;
server_name _;
return 444;
}`
/www/server/panel/vhost/nginx/xxx.com.conf
`
proxy_cache_path /www/server/fastcgi_cache/xxx.com levels=1:2 keys_zone=xxx_com_cache:10m inactive=60m;
server
{
listen 443 ssl;
listen 443 quic;
listen 80;
http2 on;
http3 on;
server_name xxx.com www.xxx.com;
index index.php index.html index.htm;
root /www/wwwroot/xxx.com/www/;
include /www/server/panel/vhost/nginx/extension/xxx.com/*.conf;
#PHP-INFO-START\s+PHP reference configuration, allowed to be commented, deleted or modified
#include enable-php-85.conf;
#PHP-INFO-END
#SSL-START SSL related configuration, do NOT delete or modify the next line of commented-out 404 rules
#error_page 404/404.html;
#HTTP_TO_HTTPS_START
if ($server_port !~ 443){
rewrite ^(/.*)$ https://$host$1 permanent;
}
#HTTP_TO_HTTPS_END
ssl_certificate /www/server/panel/vhost/cert/xxx.com/fullchain.pem;
ssl_certificate_key /www/server/panel/vhost/cert/xxx.com/privkey.pem;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers EECDH+CHACHA20:EECDH+CHACHA20-draft:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5;
ssl_prefer_server_ciphers on;
ssl_session_tickets on;
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 10m;
add_header Strict-Transport-Security "max-age=31536000";
add_header Alt-Svc 'quic=":443"; h3=":443"; h3-29=":443"; h3-27=":443";h3-25=":443"; h3-T050=":443"; h3-Q050=":443";h3-Q049=":443";h3-Q048=":443"; h3-Q046=":443"; h3-Q043=":443" ma=86400' always;
error_page 497 https://$host$request_uri;
#SSL-END
#REWRITE-START URL rewrite rule reference, any modification will invalidate the rewrite rules set by the panel
# include /www/server/panel/vhost/rewrite/xxx.com.conf;
#REWRITE-END
#ERROR-PAGE-START Error page configuration, allowed to be commented, deleted or modified
#error_page 404 /404.html;
#error_page 502 /502.html;
#ERROR-PAGE-END
location / {
proxy_pass http://127.0.0.1:8288;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header REMOTE-HOST $remote_addr;
proxy_set_header SERVER_PROTOCOL $server_protocol;
proxy_set_header HTTPS $https;
proxy_http_version 1.1;
proxy_set_header Upgrade $connection_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header REMOTE_ADDR $remote_addr;
proxy_set_header REMOTE_PORT $remote_port;
# NGINX-CACHE-START
proxy_cache xxx_com_cache;
proxy_cache_key "$scheme$host$request_uri";
proxy_cache_valid 200 301 302 2m;
proxy_cache_valid 404 1m;
proxy_ignore_headers Cache-Control Expires Vary;
proxy_cache_use_stale error timeout updating http_500 http_502 http_503 http_504;
proxy_cache_background_update on;
proxy_cache_lock on;
proxy_cache_revalidate on;
# You can configure your own website caching policy here
set $skip_cache 0;
if ($request_method = POST) { set $skip_cache 1; }
if ($query_string != "") { set $skip_cache 1; }
if ($request_uri ~* "/(cart|checkout|my-account|order|account|login|register|wp-admin|dashboard|xmlrpc.php|wp-login.php)") {
set $skip_cache 1;
}
if ($http_cookie ~* "comment_author|wordpress_[a-f0-9]+|wp-postpass|wordpress_no_cache|wordpress_logged_in|woocommerce_items_in_cart|woocommerce_cart_hash|wp_woocommerce_session_") {
set $skip_cache 1;
}
proxy_no_cache $skip_cache;
proxy_cache_bypass $skip_cache;
proxy_cache_bypass $http_upgrade;
proxy_buffer_size 256k;
proxy_buffers 4 128k;
proxy_busy_buffers_size 256k;
proxy_temp_file_write_size 256k;
add_header X-Cache "$upstream_cache_status";
add_header X-Frame-Options SAMEORIGIN;
# NGINX-CACHE-END
}
# Forbidden files or directories
location ~ ^/(\.user.ini|\.htaccess|\.git|\.env|\.svn|\.project|LICENSE|README.md)
{
return 404;
}
location ~ \.well-known{
allow all;
root /www/wwwroot/xxx.com/www/;
try_files $uri =404;
}
#Prohibit putting sensitive files in certificate verification directory
if ( $uri ~ "^/\.well-known/.*\.(php|jsp|py|js|css|lua|ts|go|zip|tar\.gz|rar|7z|sql|bak)$" ) {
return 404;
}
access_log /www/wwwlogs/xxx.com.log;
error_log /www/wwwlogs/xxx.com.error.log;
#Monitor-Config-Start Website monitoring report log sending configuration
access_log syslog:server=unix:/tmp/bt-monitor.sock,nohostname,tag=6__access monitor;
error_log syslog:server=unix:/tmp/bt-monitor.sock,nohostname,tag=6__error;
#Monitor-Config-End
}`